1. What is GuardDuty?
Amazon GuardDuty is an intelligent threat detection service that continuously monitors your AWS accounts and workloads for malicious activity and unauthorized behavior using machine learning, anomaly detection, and integrated threat intelligence.
Core Concept
GuardDuty = intelligent threat detection. One click to enable. No software to install, no infrastructure to manage. It analyzes billions of events across multiple data sources and generates security findings when it detects threats. Think: automated security analyst watching your account 24/7.
2. Data Sources
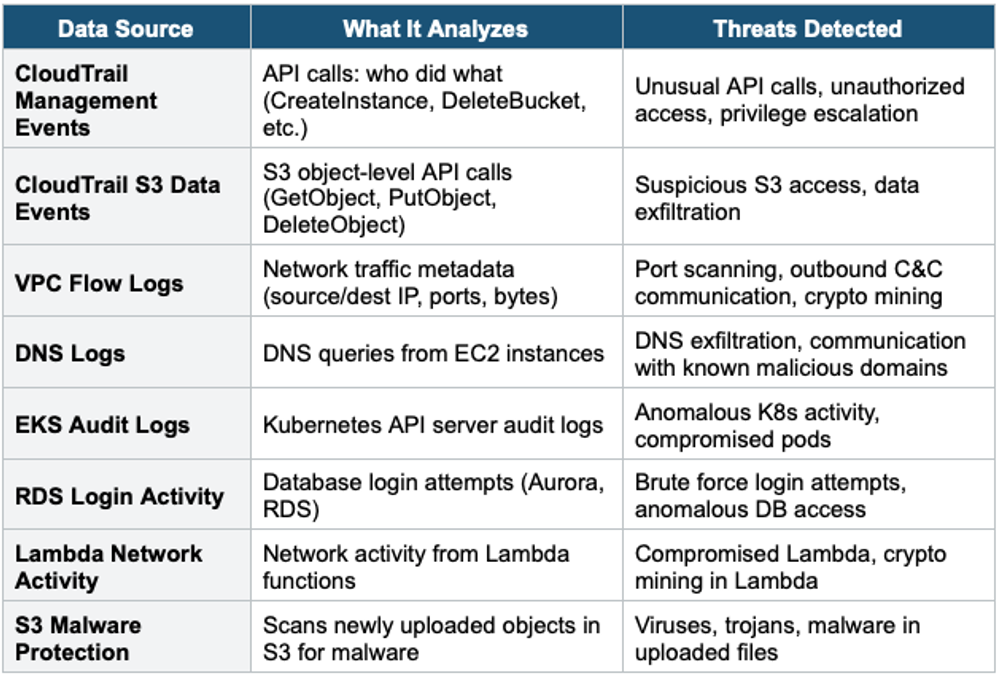
- GuardDuty does NOT require you to enable Flow Logs, CloudTrail, or DNS Logs separately — it accesses them independently
- No performance impact on your resources
3. GuardDuty Findings
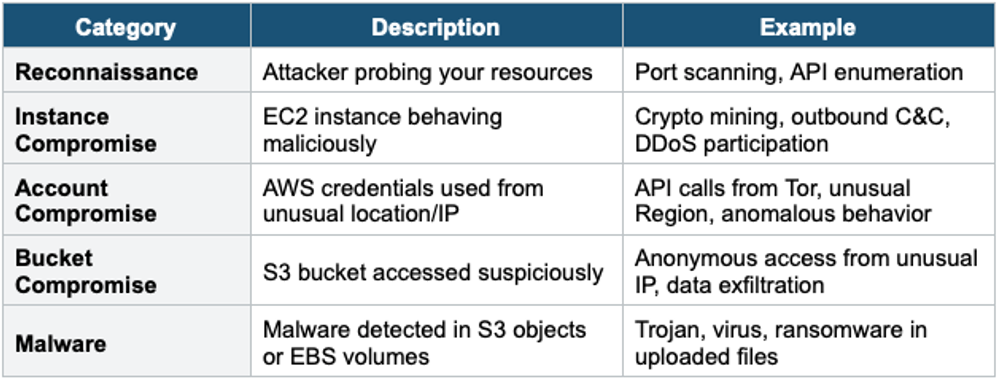
- Findings are potential security issues rated by severity: Low, Medium, High
- Finding types follow the pattern: ThreatPurpose:ResourceType/ThreatFamilyName.DetectionMechanism
- Examples: Recon:EC2/PortProbeUnprotectedPort, CryptoCurrency:EC2/BitcoinTool.B, UnauthorizedAccess:IAMUser/MaliciousIPCaller
- Findings sent to: GuardDuty Console, EventBridge (for automation), Security Hub
Common Finding Categories
4. GuardDuty Automation
Common GuardDuty Automation Pattern:
GuardDuty Finding (High Severity)
→ EventBridge Rule (match finding type + severity)
→ Lambda Function
→ Remediation actions:
- Block IP in NACL or WAF
- Isolate EC2 instance (modify SG to deny all)
- Disable compromised IAM access keys
- Send alert to SNS / Slack / PagerDuty
- Create a JIRA ticket5. GuardDuty Key Features
- Multi-account: enable across AWS Organization via delegated administrator
- Multi-Region: must be enabled in each Region separately
- 30-day free trial. Pay per volume of data analyzed after trial.
- Trusted IP List: IPs that should never generate findings (your office IPs)
- Threat IP List: custom list of known-bad IPs to flag
- Suppression Rules: auto-archive low-priority findings matching specific patterns
- Malware Protection: scans EBS volumes attached to potentially compromised instances
Exam Tip
GuardDuty: "Intelligent threat detection" = GuardDuty. "Detect crypto mining on EC2" = GuardDuty. "Detect compromised credentials" = GuardDuty. "Detect malware in S3" = GuardDuty S3 Malware Protection. No agents to install. One-click enable. Analyzes CloudTrail, VPC Flow Logs, DNS, EKS, RDS, Lambda, and S3. Automate with EventBridge → Lambda.