1. What is AWS Network Firewall?
AWS Network Firewall is a managed stateful firewall and intrusion detection/prevention service (IDS/IPS) for your VPC. It provides deep packet inspection, protocol detection, and domain-based filtering at the network level (Layer 3–7).
Core Concept Network Firewall sits INSIDE your VPC and inspects all traffic entering or leaving the VPC. Unlike WAF (which only inspects HTTP/HTTPS at Layer 7), Network Firewall inspects ALL protocols at Layers 3–7: TCP, UDP, ICMP, and more. It provides IDS/IPS capability (detect and block malicious traffic patterns) that WAF and Security Groups cannot.
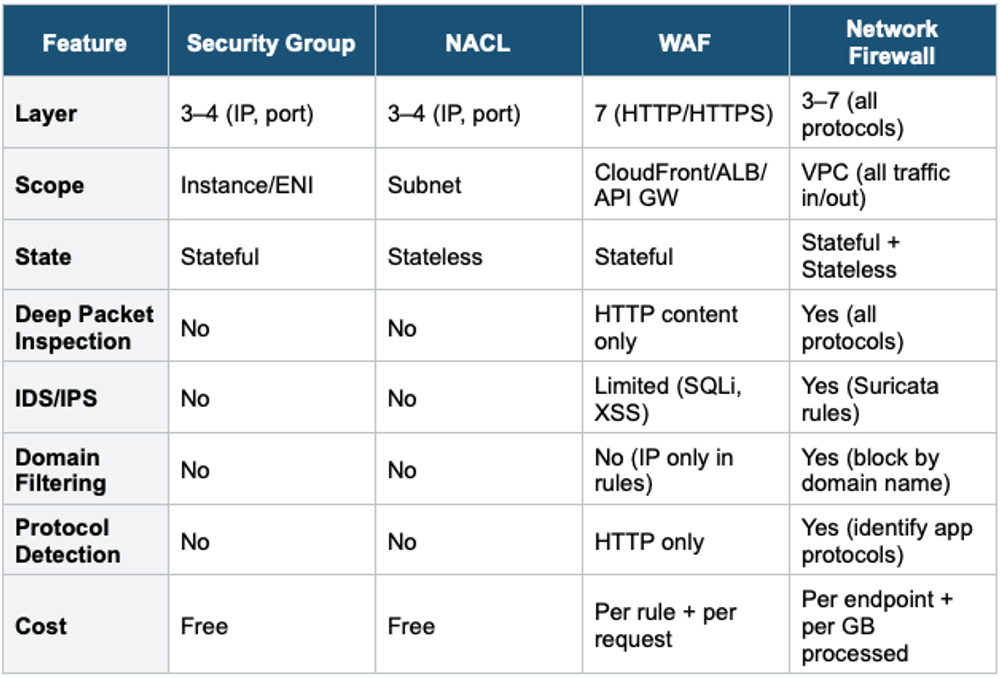
2. Network Firewall vs Other Security Services
3. Network Firewall Architecture
Network Firewall Placement in VPC:
Internet
|
IGW
|
Firewall Subnet (Network Firewall Endpoint)
|
Public Subnet (ALB, NAT Gateway)
|
Private Subnet (App Servers, Databases)
Traffic flow (ingress):
Internet → IGW → Firewall Endpoint → ALB → App
Traffic flow (egress):
App → Firewall Endpoint → NAT GW → IGW → Internet
Route tables direct traffic through the firewall endpoint.
The firewall inspects ALL traffic passing through it.- Network Firewall Endpoint is deployed in a dedicated "firewall subnet."
- Route tables in IGW and application subnets route traffic through the firewall endpoint
- Deploy one endpoint per AZ for high availability
- All traffic (inbound AND outbound) passes through the firewall for inspection
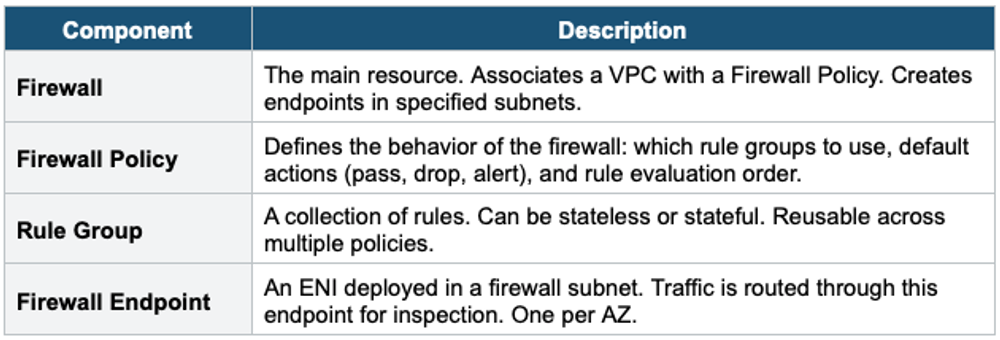
4. Network Firewall Components
5. Rule Types
Stateless Rules
- Evaluated based on: source/destination IP, source/destination port, protocol
- No connection tracking (like NACLs, but more powerful)
- Evaluated FIRST, in priority order
- Actions: Pass (send to stateful engine), Drop, Forward to stateful rule group
- Use for: bulk filtering known-bad traffic before deeper inspection
Stateful Rules
- Connection-aware (tracks connection state like Security Groups)
- Three rule formats:
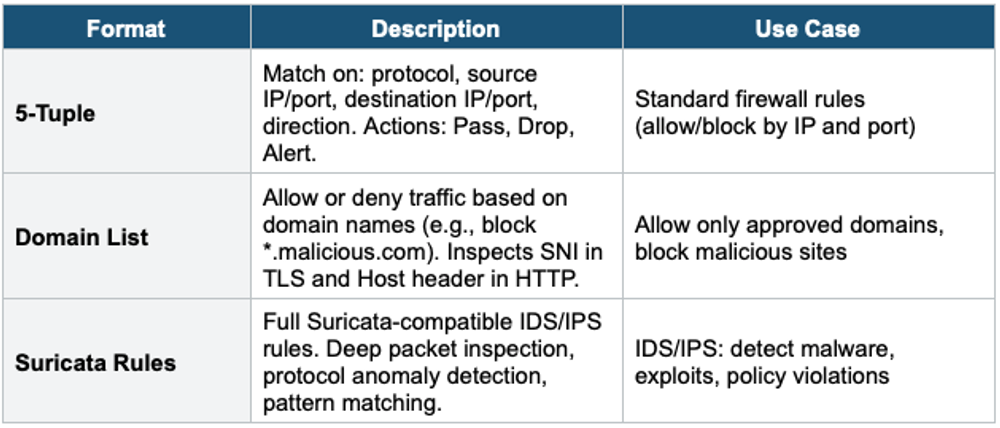
Suricata IDS/IPS Suricata is an open-source intrusion detection/prevention engine. AWS Network Firewall uses Suricata rules natively. You can write custom Suricata rules or use AWS-managed threat intelligence rule groups. Suricata rules can inspect packet payloads, detect malware signatures, identify application protocols, and more — far beyond what Security Groups or NACLs can do.
6. Domain Filtering
One of the most powerful features of Network Firewall is domain-based filtering:
- Allow ONLY traffic to approved domains (allowlist)
- Block traffic to known-bad domains (denylist)
- Works for HTTP (inspects Host header) and HTTPS (inspects SNI in TLS handshake)
- Does NOT decrypt TLS — inspects the unencrypted SNI field
Domain Filtering Example: Allowlist: .amazonaws.com (allow all AWS services) .github.com (allow GitHub) .ubuntu.com (allow Ubuntu repos) All other domains: BLOCKED This prevents data exfiltration to unauthorized domains, command-and-control callbacks, and access to unauthorized sites.
7. Network Firewall Logging
- Alert logs: records when a stateful rule generates an alert (suspicious traffic)
- Flow logs: record metadata about all traffic processed by the firewall
- TLS logs: records TLS handshake metadata
- Destinations: S3, CloudWatch Logs, Kinesis Data Firehose
- Use for: security monitoring, incident investigation, compliance auditing
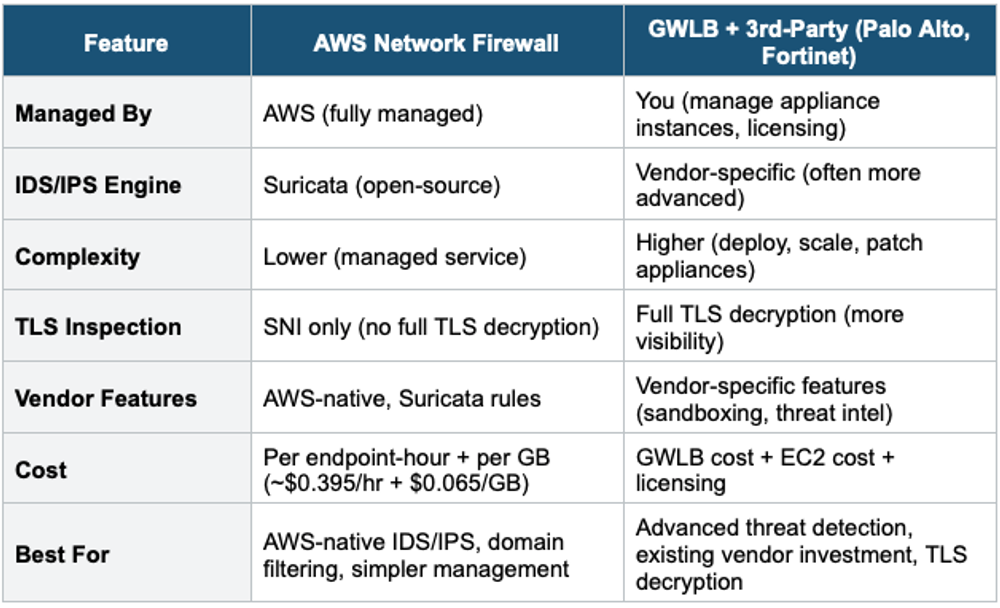
8. Network Firewall vs GWLB + Third-Party Appliances
9. Route 53 Resolver DNS Firewall
While not part of AWS Network Firewall, DNS Firewall is a related network security service:
- Filters outbound DNS queries from your VPC
- Block or allow DNS resolution for specific domain names
- Prevents DNS-based data exfiltration (tunneling data through DNS queries)
- Uses domain lists: AWS-managed threat lists or your custom lists
- Actions: Allow, Block (return NXDOMAIN or custom response), Alert
- Managed via Firewall Manager across the organization
- Free for AWS-managed domain lists. Charged for query processing.
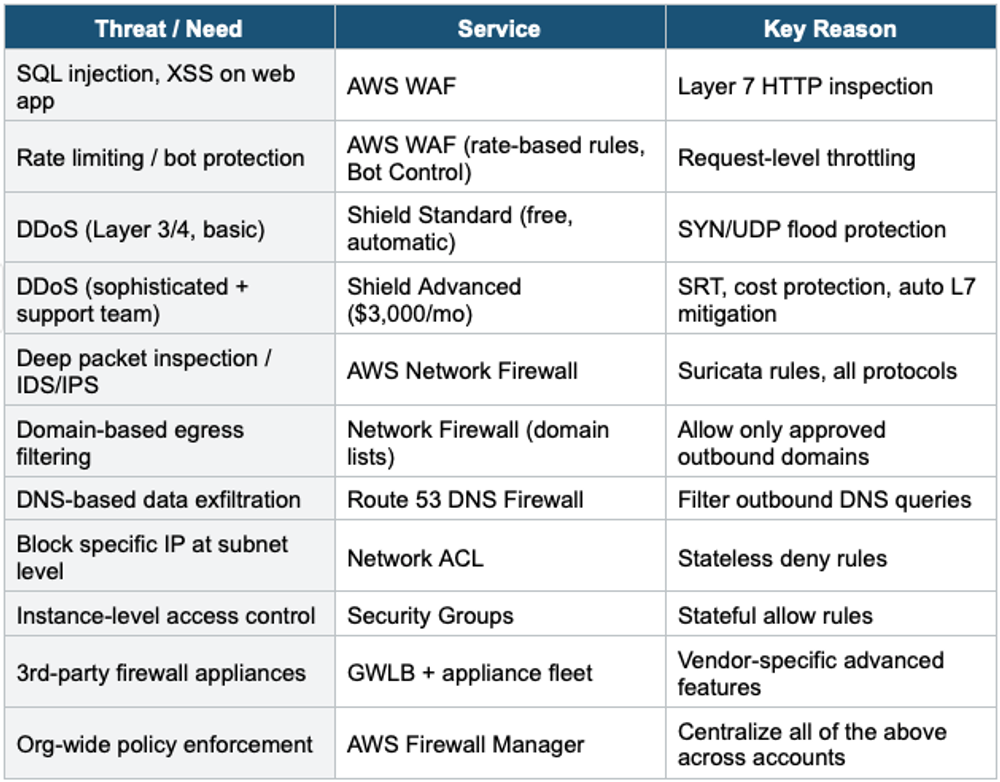
10. Complete Network Security Decision Table
Exam Tip Network Firewall: "VPC-level IDS/IPS" = Network Firewall. "Deep packet inspection" = Network Firewall (Suricata). "Block by domain name" = Network Firewall domain lists. "DNS filtering" = Route 53 DNS Firewall. NF sits in a dedicated firewall subnet. Route tables direct traffic through firewall endpoints. NF vs GWLB: NF = managed Suricata; GWLB = bring your own appliance. NF does NOT do full TLS decryption (SNI only).